Deploy Defused across IT, OT, cloud, or on-premise environments with just a few clicks. The platform is designed for quick setup, allowing your first deployment to be up and running in less than 30 minutes.
As we move towards 2025, Defused can help with top cybersecurity priorities by strengthening Zero Trust architectures, securing hybrid-cloud environments, building automation and providing high-quality data for AI initiatives.
Defused helps reduce attack surfaces, enhance visibility, prevent lateral movement, and streamline threat detection and response. Equip your organization with Defused to effectively be in sync with what is happening in the threat and vulnerability landscape.
Core features of Defused
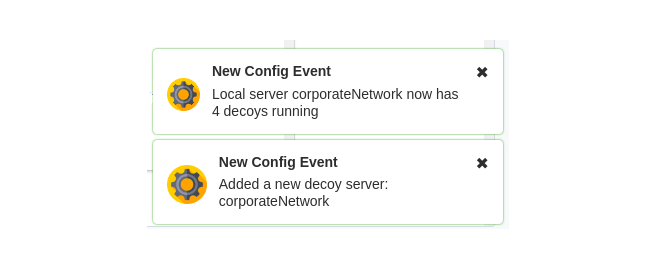
Deploy Defused across IT, OT, cloud, or on-premise environments with just a few clicks. The platform is designed for quick setup, allowing your first deployment to be up and running in less than 30 minutes.
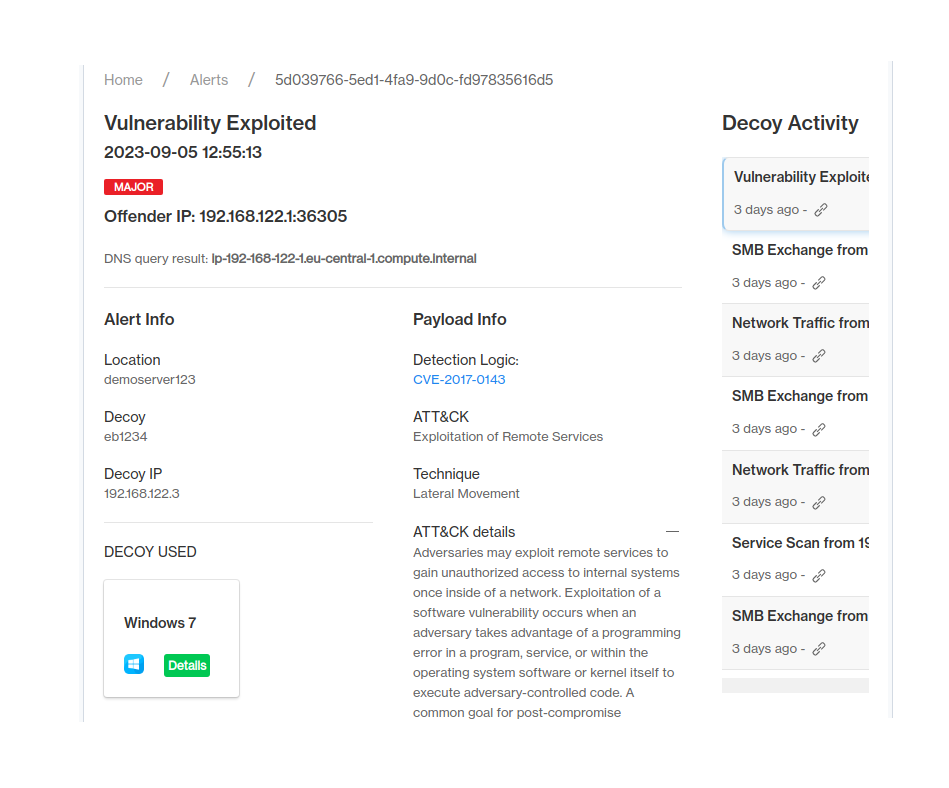
Reduce alert fatigue with accurate and context-rich alerts. Defused's decoy systems are designed to attract genuine threats, providing your security team with actionable intelligence.

Defused offers a wide range of integration options to enhance your existing security workflows. Automate responses and optimize configurations by connecting Defused with your preferred tools.
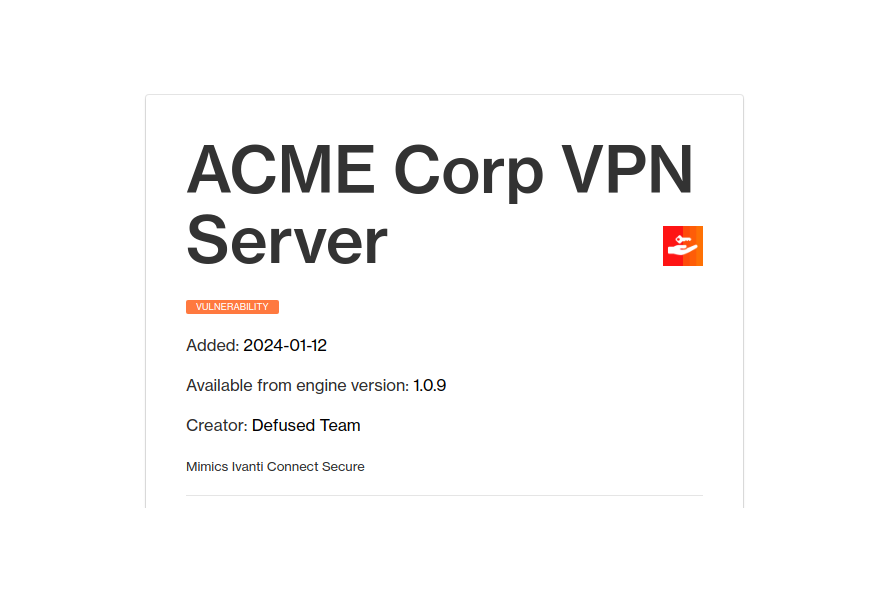
Protect diverse digital environments, including legacy systems, industrial networks, and medical devices. Defused ensures robust security across all platforms.
As we move towards 2025, Defused can help organizations address the top cybersecurity priorities by strengthening Zero Trust architectures, securing hybrid-cloud environments, building automation, and providing high-quality data for AI initiatives.
Optimize Defused configurations and create robust security automation routines by integrating with your existing tools:
 Email
Email ServiceNow
ServiceNow SIEM Systems
SIEM Systems Tines Automation
Tines Automation Slack
Slack EDR Solutions
EDR Solutions Vulnerability Management
Vulnerability Management Active Directory
Active DirectoryRead more about our integrations in the Defused documentation.
First deployment up and running in less than 30 minutes