Defused EX
Honeypots on your perimeter. Managed by us. Catching real attacks targeting your edge.
Deploy EX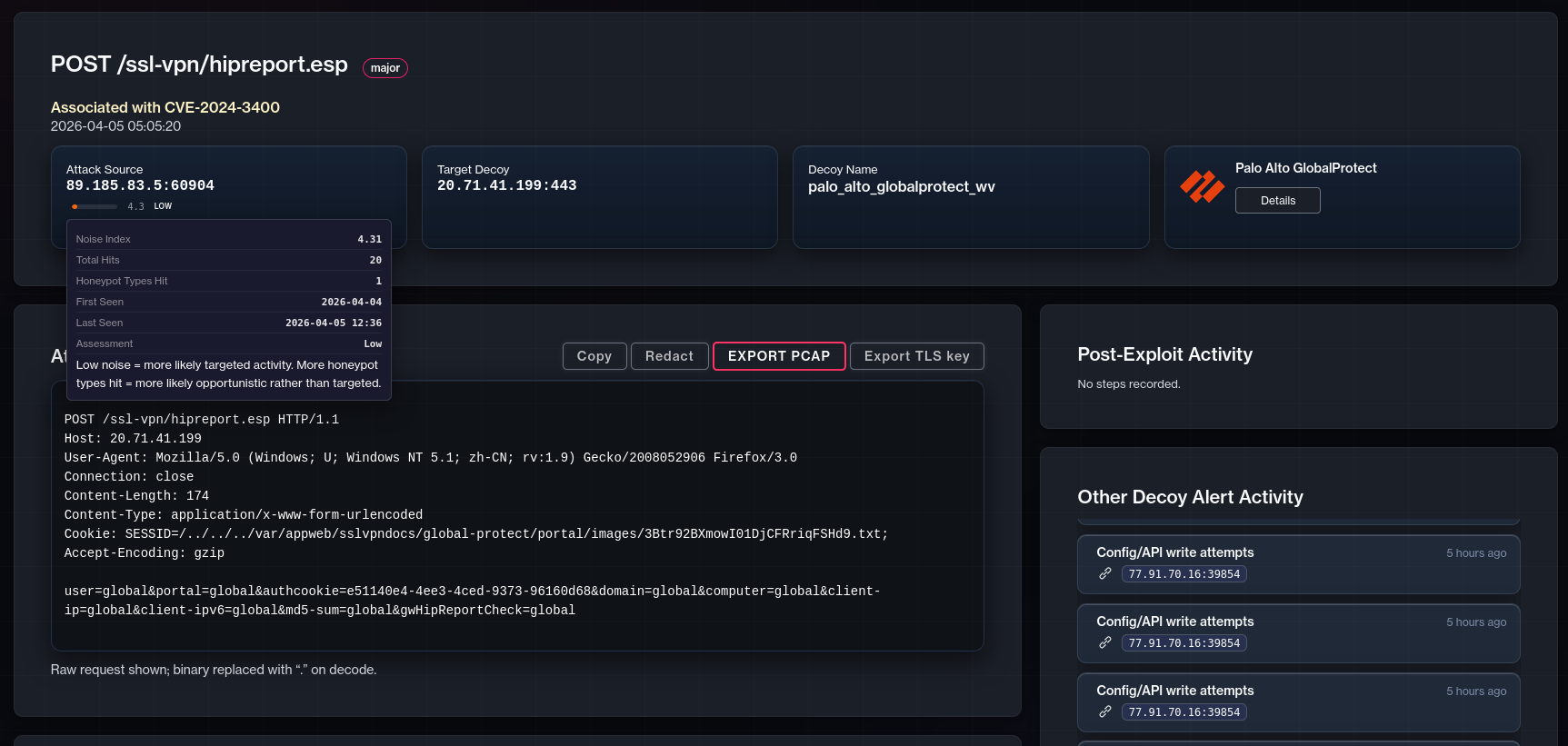
Key Capabilities
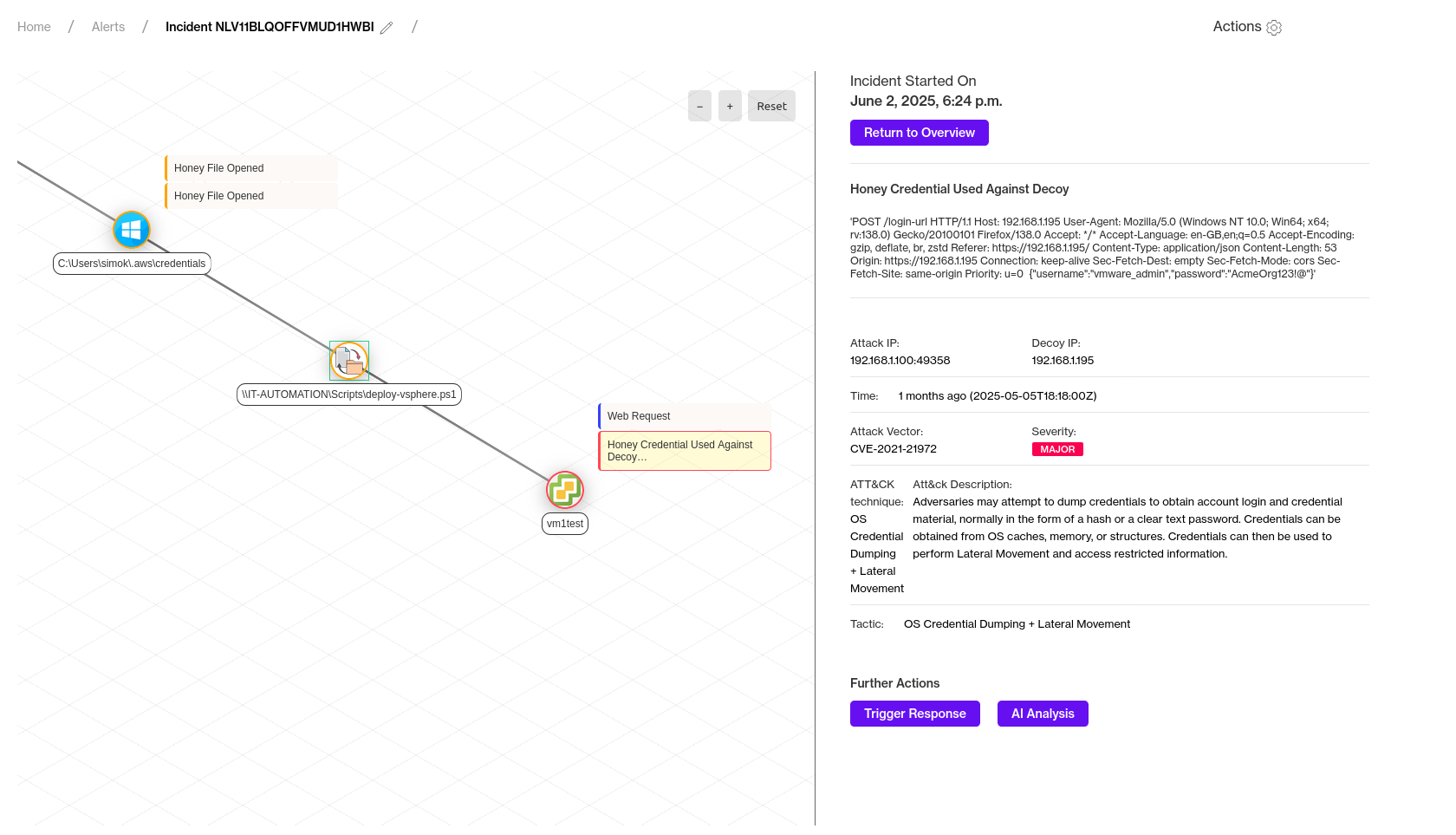
Catch attackers at the door
Honeypots sit alongside your VPNs, firewalls, and gateways. Every hit is auto-compared against our global TF feed - scanners are flagged, what's left is traffic targeting you specifically.
You deploy, we run
Choose your geolocation, brand decoys with your own logos and assets, and let Defused handle everything else - updates, hardening, uptime.
Full payload capture
Every attack is recorded with IOCs, malware samples, and tooling. Not just an alert - the evidence behind it.
Operational Outcomes
Signal before breach
See attacker activity while they're still probing - before credentials or controls are compromised.
Less noise, faster triage
Honeypot alerts are high-fidelity by nature. Auto-comparison to TF strips out the background noise so you only see what matters.
Know what they're after
See exactly which edge services are being targeted and how - context your SOC can act on immediately.
Your perimeter is already being probed
Defused EX makes that activity visible - high-fidelity alerts from managed honeypots, zero deployment burden.
Deploy EX